The Risks of Breaching Confidentiality in Investigative Work
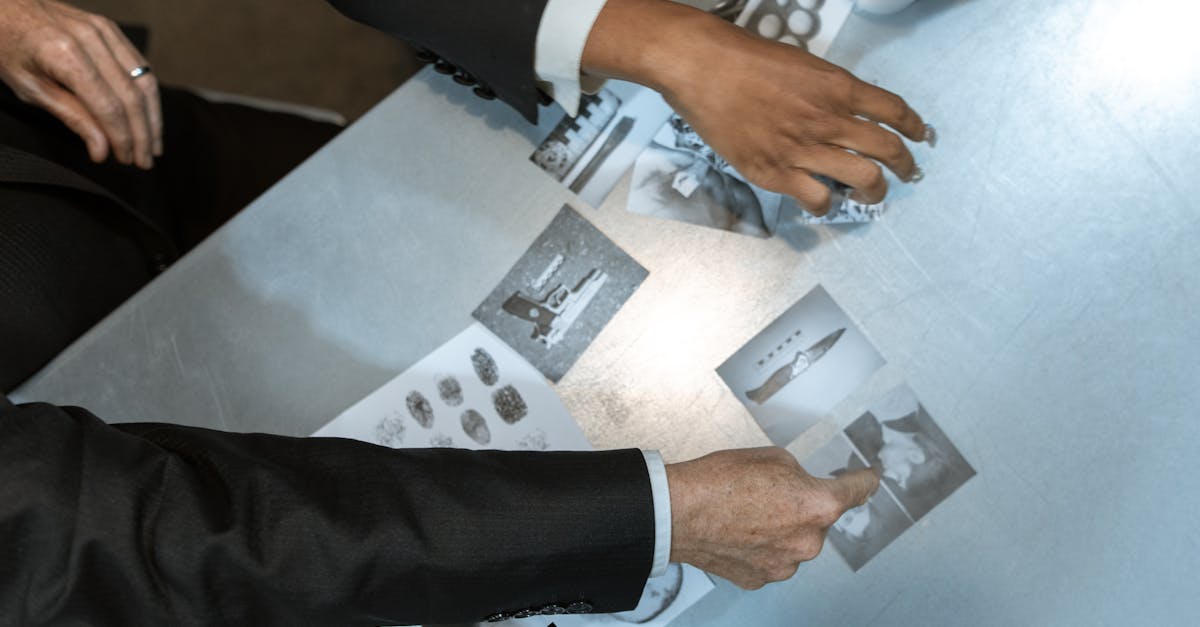
Table Of Contents
Strategies for Protecting Confidential Information
Confidentiality is paramount in investigative work, and various strategies are essential for its protection. One effective approach involves limiting access to sensitive information only to those who genuinely need it for the investigation. This ensures that even within a team, the risk of exposure is minimised. Additionally, implementing robust data storage solutions, such as encrypted file systems or secure cloud-based services, enhances security and prevents unauthorised access from both internal and external threats.
Another vital aspect is the establishment of clear protocols for handling confidential information. Providing investigators with explicit guidelines on what constitutes confidential data and appropriate methods of communication can significantly reduce risks. Regular audits and assessments of these processes help identify potential vulnerabilities. Building a culture of confidentiality within the organisation encourages all team members to prioritise safeguarding sensitive information effectively.
Best Practices for Investigators
Maintaining a strict code of conduct is essential in investigative work. Investigators should establish clear guidelines for handling confidential information. Regularly reviewing and updating these protocols can help mitigate risks associated with breaches. It is crucial to limit access to sensitive data only to those who require it for their role. This approach reduces the likelihood of inadvertent exposure.
Another important practice involves thorough documentation of all activities related to confidential cases. Keeping detailed records helps track information flow and communications. Secure storage for both physical and digital documents is necessary. Using encrypted systems for digital records further enhances security. Additionally, conducting regular audits can identify potential vulnerabilities and ensure compliance with established confidentiality measures.
Training and Awareness for Investigators
Education plays a crucial role in equipping investigators with the necessary skills to manage sensitive information. Adequate training should encompass not only the legal aspects of confidentiality but also practical techniques for safeguarding data. Investigators must be familiar with potential threats and understand the importance of establishing secure communication channels. Regular workshops and refresher courses can help keep their knowledge current and relevant.
Creating a culture of awareness is equally significant in fostering a secure environment. When investigators are mindful of confidentiality's importance, they are more likely to adhere to best practices. Encouraging open discussions about challenges faced in the field can enhance team collaboration. A commitment to ongoing training and awareness contributes to an ethos where the protection of confidential information becomes a fundamental part of daily operations.
The Role of Ongoing Education
Continuous education is vital for investigators in maintaining a robust understanding of confidentiality and ethical standards. Regular training sessions can keep professionals informed about the latest laws, regulations, and best practices regarding data protection. Emphasis on real-life scenarios during training helps illustrate the potential consequences of breaches. This practical approach equips investigators with the skills required to navigate complex situations effectively.
Furthermore, ongoing education fosters a culture of accountability within investigative teams. Employees who are well-versed in confidentiality protocols are more likely to be vigilant and proactive in their day-to-day work. Encouraging discussions about recent developments in the field can strengthen team cohesion while reinforcing the importance of confidentiality. Investing in regular learning opportunities not only enhances individual performance but also contributes to the overall integrity of the investigative process.
Technological Solutions for Confidentiality
Modern investigators often rely on a range of technological tools designed to bolster confidentiality in their work. Secure communication applications provide end-to-end encryption, ensuring that sensitive discussions remain private. Additionally, cloud storage solutions with robust security measures allow for safe sharing of documents among team members while protecting against unauthorised access. Implementing these technologies helps safeguard valuable information and maintain client trust.
Furthermore, biometric security measures, such as fingerprint or facial recognition systems, offer an extra layer of protection for accessing sensitive data. Two-factor authentication has become a standard practice to verify user identities before granting access to privileged information. Regular software updates and strong password protocols also play essential roles in mitigating vulnerabilities. By utilising these technological advancements, investigators can better navigate the complex landscape of confidentiality in their work.
Tools and Software to Enhance Security
The landscape of investigative work is becoming increasingly reliant on advanced technological solutions to safeguard confidential information. A variety of tools are available, ranging from encrypted communication apps to secure file-sharing platforms. These applications ensure that sensitive data remains protected, making it difficult for unauthorised parties to access crucial information. Implementing these tools not only enhances security but also builds trust with clients who expect their information to be handled with utmost care.
In addition to communication and file-sharing solutions, specialised software designed for data management plays a vital role in maintaining confidentiality. Such programmes help investigators organise and analyse data while enforcing strict access controls. Features like audit trails provide accountability, capturing any modifications or attempts to access sensitive files. Adopting a multi-layered approach that incorporates various tools and software creates a more resilient defence against potential breaches.
FAQS
What are the main risks associated with breaching confidentiality in investigative work?
The main risks include legal repercussions, loss of trust from clients, potential harm to individuals involved, and damage to the reputation of the investigative agency.
How can investigators protect confidential information?
Investigators can protect confidential information by implementing best practices such as secure data storage, limiting access to sensitive information, and using secure communication channels.
What types of training should investigators undergo regarding confidentiality?
Investigators should undergo training that covers legal requirements, ethical considerations, and the importance of confidentiality, as well as practical training on using security tools and software.
Why is ongoing education important for investigators?
Ongoing education is important as it keeps investigators updated on the latest legal regulations, technological advancements, and best practices for maintaining confidentiality.
What technological solutions can help enhance confidentiality in investigative work?
Technological solutions include encryption software, secure file-sharing platforms, password management tools, and secure communication apps designed to protect sensitive information.
Related Links
Protecting Sensitive Information: Best Practices for InvestigatorsDiscretion in Surveillance: Why It Matters for Clients
The Importance of Non-Disclosure Agreements in Investigations
Building Trust Through Confidentiality with Private Investigators
The Impact of Discretion on the Outcome of Infidelity Cases
How Confidentiality Enhances the Investigation Process
Discretion Strategies for Private Investigators in Sydney
Maintaining Client Privacy: A Guide for Private Investigators
The Essential Role of Confidentiality in Infidelity Investigations